Essential Tips for Averting Common Security Threats
Dealing with security threats is an unfortunate and all too common reality for businesses, institutions and private individuals. Despite the efforts invested in prevention, threats and potential risks are inherent in our day-to-day operations. Safety starts with awareness and understanding, and by being proactive in security measures, companies can reduce their vulnerabilities. As such, understanding and expected risks and threats can help build precautionary steps for security in both prospective and offhanded scenarios.
But where to start? This article provides essential security advice for avoiding major security challenges when engaging in personal or business operations, from utilising security systems to consulting with security professionals.
Incorporate Security Technologies
When it comes to security, technology offers an array of selectable and customisation solutions. Installing the appropriate technologies can supplement and optimise the effectiveness of your security measures; in fact, automation may first and foremost come up in the minds of security administrators — and for good reason.
From access control gates to surveillance cameras and alarm systems, security technology is designed to detect and alert personnel to unusual activities occurring on and off the premises. Fit for connecting and automating different systems, many of the top tools integrate with today’s most popular data mediums and facilitate maintenance and supervision of large-scale security operations.
Likewise, many of today’s premier security technologies employ analytics to anticipate potential risks or threats. This feature also allows admins to keep up a comprehensive audit trail of employee and customer activities, enabling total oversight over daily operations. What’s more, these applications also support customised alerts sent straight to one’s phones.
Seek Support from Security Professionals
Be it an online store, an educational institution, or a governmental office, employing security guards to supplement one’s security plans for the purpose of deterring crime is an optimal decision. In a nut shell, security guards are professionals who are highly trained to remain highly alert and aware and to establish security protocol among customers and personnel.
When selecting a security service provider, however, consider doing a background check of both the services they claim to provide as well as their cost standings. Services such as comprehensive patrol operations and screening programs are only a few resources offered by companies entailed in the security niche. Oversight of electronic containment systems and assessment of personnel activities may also be expected.
Along with the services rendered, ensure the security personnel offered also meets your company’s preference. Sufficiently trained guards improve regulatory compliance, and warn of any pending issues. Presentation is just as important; starting with a database search while hire certified guards for best results.
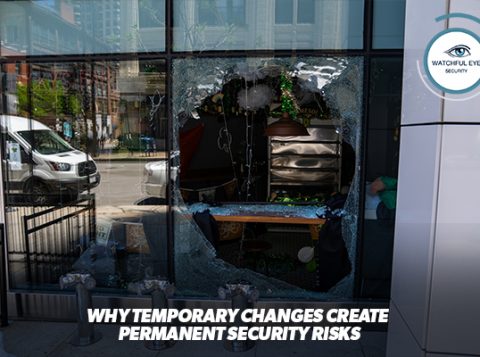
Utilize Crisis Response Methods
Almost all emergency case scenarios require some level of immediate response — be it in the physical or digitally backed form. Professional barriers — from multiple authentication passwords to physical access — help protect assets and safeguard people’s lives.
One will also want to implementing incident response plan (IRP). This plan should involve three steps for acting on disruptions: detection, assessment and response. A well-prepared response plan should also contain a backup set of procedures that an organization may leverage should the primary strategies fail; these could be based on prior experience or research. Services such as drills and interactive testing ensure participants are aware of reaction topics and instructions.
Finally, one may also want to look into an incident response monitor. By installing this type of system, admins can be alerted to unauthorized activity while streamlining its response. This includes removing or disabling access rights, alter user access levels, as well as other Tesla-like commands.
These methods and techniques will not only reduce the risk of cyber-attack, but also limit potential damage if a hazardous situation does occur.
No matter the security risk, speed and accuracy are essential parts of crisis response procedures. That’s why taking proactive steps in safeguarding one’s business and mission by employing security systems and seeking support from security guards can be a way to ensure a safe environment. Invest the resources necessary for curtailing risks and threats, and bolstering the security of your office or business association. Risk detection systems, guards, and IRps are pivotal components in formulating your security plan. Implementing these components can bring your defence to the next level while avoiding adverse querulous outcomes.